Our Blog
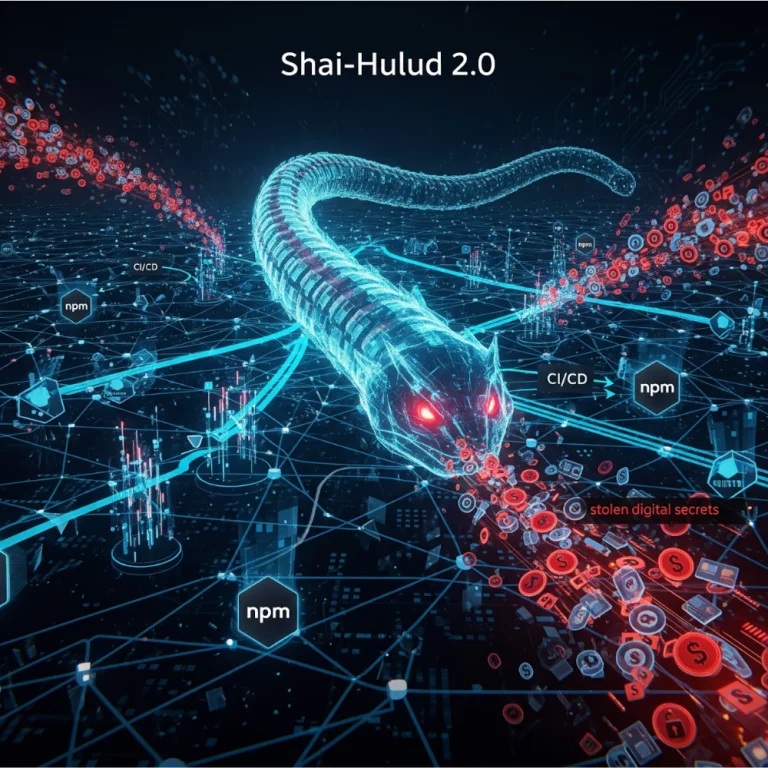
The Shai-Hulud 2.0 npm worm is one of those incidents that AppSec teams will be referencing in post-mortems for years. Let’s analyze what happened, who was impacted, and how a SSCS platform like ScribeHub could have helped organizations prevent or at least dramatically limit the blast radius. 1. What is Shai-Hulud 2.0? Shai-Hulud first appeared […]
Read more
TL;DR — A self-replicating npm “worm” dubbed Shai-Hulud poisoned popular packages, stole developer/CI secrets, and then used those secrets to publish more malicious versions, turning victims into new propagation points. Within hours of the disclosures, Scribe ran portfolio-wide checks across our customers’ SBOMs and build attestations and confirmed their pipelines were not pulling any compromised […]
Read more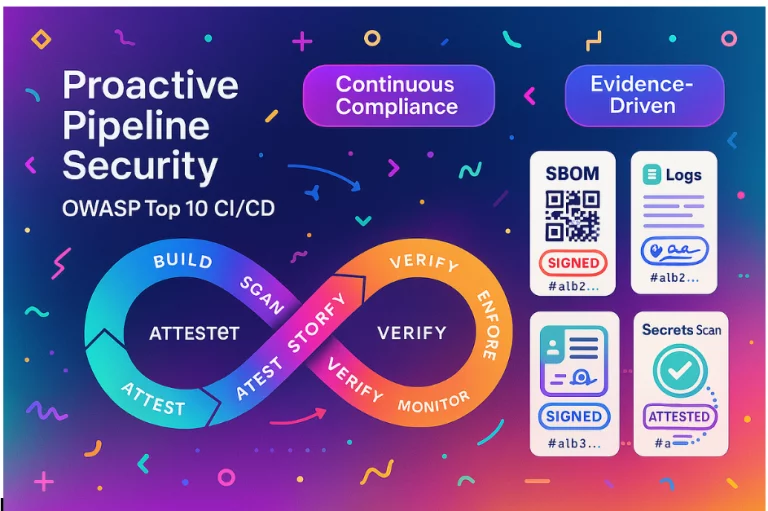
This article was co-written by Mikey Strauss and Viktor Kartashov. Turn OWASP Top 10 risks into automated, auditable controls In modern DevOps environments, CI/CD pipelines are the backbone of software delivery. But with great speed comes great exposure. As organizations accelerate releases, attackers are increasingly targeting insecure pipelines to inject malicious code, exfiltrate secrets, or […]
Read more
From Static Reports to Conversational Security Security teams today are drowning in data: SBOMs, CVEs, xAST results, compliance checks and risk dashboards. But insights often stay locked in dashboards that only a few experts know how to query. At Scribe Security, we believe your security data should be as accessible as a conversation. That’s why […]
Read more
It starts the same way in almost every engineering team. Developers are moving fast, building features, integrating third-party packages, and now, writing code with AI copilots. The CI/CD pipelines are humming day and night, pushing updates to production faster than ever. Customers are happy with the speed. But in the back of every CISO’s mind […]
Read more
Your Vibe Coding Project is Infested with Vulnerabilities! Building software with AI has gone from science fiction to everyday reality. Your AI-coded project may work perfectly… until hackers find the flaws. In this post, we will cover the way from AI-generated code full of findings and vulnerabilities to a trusted product by walking through an […]
Read more
Imagine the workload on a developer: a long day of coding, deadlines looming, and then the dreaded SAST report arrives. Hundreds of findings, each one a potential vulnerability, each one requiring careful attention. The process is repetitive, time-consuming, and, let’s be honest, sometimes a demoralizing drudgery. And the situation is only getting worse; code generation […]
Read more
This article was do-written with Viktor Kartashov and Daniel Nebenzahl. The Auditor’s Litmus Test: Can You Prove Your Builds? “Can you prove, definitively, that every container image you ship was built exactly the way you claim?” Most auditors expect a swift, confident answer – not weeks of frantic YAML refactoring. The SLSA (Supply-chain Levels for […]
Read more
Co-written with Viktor Kartashov. The NIST SP 800–190 standard provides structured guidelines to secure containerized applications , covering everything from image provenance to runtime controls. As container use explodes in fast-paced DevOps environments, aligning with these requirements becomes both essential and challenging. But SP 800–190 here is just a use case . The bigger idea is to […]
Read more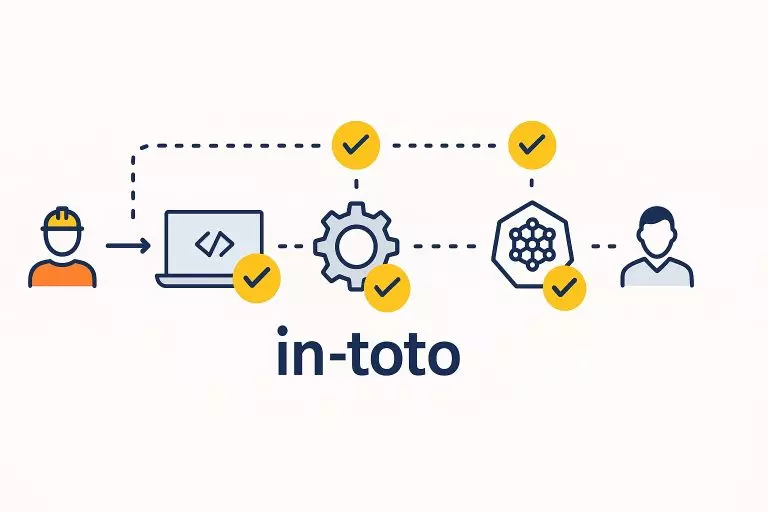
What Is in-toto and How Does It Protect the Software Supply Chain? Software supply chain attacks, like those seen in recent years – 3CX, Codecov, and Solarwinds – have highlighted the fragility of traditional development pipelines. In response, the open-source community developed in-toto, a framework to ensure integrity at every step of software delivery. In-toto […]
Read more