Our Blog
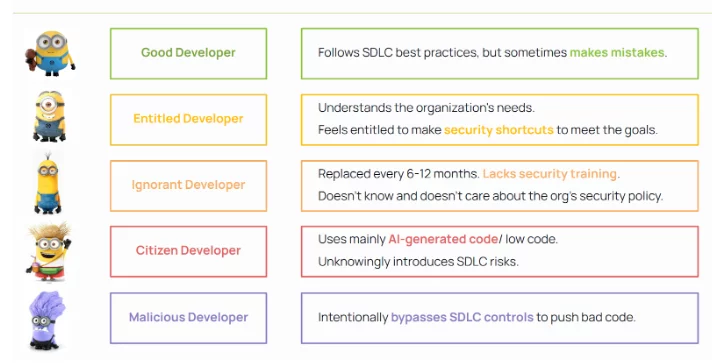
In today’s software development landscape, the diversity of developer profiles is both a strength and a vulnerability. The attached taxonomy—ranging from well-intentioned but imperfect “Good Developers” to “Citizen Developers” using AI-generated code, and even “Malicious Developers”—highlights how varying levels of experience, intent, and behavior can pose significant software development lifecycle (SDLC) risks. Scribe Security addresses […]
Read more
At Scribe Security, we believe the future of cybersecurity hinges on securing software supply chains from the inside out. That’s why we’re proud to collaborate with the National Cybersecurity Center of Excellence (NCCoE) on its Software Supply Chain and DevOps Security Practices project. This initiative convenes public and private sector technology contributors to explore how […]
Read more
Most software organizations use multiple platforms for code management, build, registry, delivery, and deployment. Governing the security of the SDLC and software supply chain requires a unified platform that extends beyond GitHub’s native capabilities. Effective risk management demands clear traceability and governance from code to cloud—ensuring every container image and released artifact is linked to […]
Read more
The landscape of federal software security is undergoing a significant transformation. In January 2025, the White House issued a new Executive Order focusing on strengthening the security and transparency of third-party software supply chains used by federal agencies. This mandate introduces crucial changes that software providers need to understand and prepare for, especially given the […]
Read more
In today’s rapidly evolving software development landscape, security and compliance have become paramount. As organizations increasingly rely on third-party components and open-source software, understanding what’s inside your software has never been more critical. Enter the Software Bill of Materials (SBOM)—a detailed list of all components, libraries, and dependencies that make up your software. Integrating SBOMs […]
Read more
In recent years, software supply chain attacks have emerged as a significant cybersecurity threat, targeting the complex networks of relationships between organizations and their suppliers. This article delves into notable recent supply chain attacks, examining how they occurred and discussing strategies for prevention and mitigation. From breaches that compromise sensitive data to attacks that exploit […]
Read more
Securing Your Software Supply Chain begins with the Discovery and Governance of Your ‘Software Factory’ In today’s software development environment, teams handle decentralized assets such as code repositories, build pipelines, and container images. While this distributed model offers flexibility and speeds up production, it also fragments assets and complicates governance and security oversight, especially as […]
Read more
With the increased complexity of software supply chains, managing and securing software components has become more challenging. To tackle this, a Software Bill of Materials (SBOM) has emerged as a crucial tool for ensuring security, transparency, and compliance in the software development lifecycle. An SBOM is a comprehensive record of all components used in creating […]
Read more
On June 20, 2024, Gartner released its influential Leader’s Guide to Software Supply Chain Security, highlighting the growing need to defend against software supply chain attacks. With these attacks’ increasing frequency and sophistication, organizations face significant risks that they must manage effectively. This post interprets the critical findings from Gartner’s report. It explains how Scribe […]
Read more
In an era where cyber threats are growing in both sophistication and scale, organizations are increasingly relying on artificial intelligence (AI) to strengthen their security frameworks. This trend is particularly significant in software supply chain security, where AI is becoming a crucial tool in identifying vulnerabilities, predicting emerging threats, and streamlining the development and deployment […]
Read more